* What is shadow IT?
“Shadow IT” is a term that refers to endpoints other than those authorized by a corporation for internal use being used by employees without permission. Shadow IT devices may not have adequate security, introducing risks of data loss, malware infections and other security issues.
Knowledge Security Column Vol.5
Shadow IT at overseas/small-scale sites threatens corporate security!

In this column’s previous article, we described how the first step in securing your IT environment is getting a grasp on what endpoints are in use, but unmanaged endpoints can connect to your company network without you knowing about it, making it difficult to know all the endpoints in use. This article will cover examples and countermeasures for “shadow IT*”, which can be an issue at the stage of trying to ascertain all endpoints in use.
Shadow IT examples
Ex1
Bringing in and using a cheap and easily configured small Wi-Fi router
Engineer A
For Wi-Fi testing at work, he brings in a small router he had at home and connects it to the company network without getting permission from the IT administrator. He also connected to the Wi-Fi router from his personal smartphone.

Ex2
Using personally-owned software at the company
Creator B
Software needed for her work was not installed on the computer provided by her company. Purchasing the software with company funds would require going through company procedures, but since she already owned the software for personal use, she instead brought her personal laptop with the software installed to work and used that.

Ex3
Password shared with coworkers
IT admin C
He was asked by a coworker for the password to the company Wi-Fi for connecting a test device, and he gave it with the intention of it being used only temporarily, but the password got shared and started being used to connect personal smartphones and computers to the company Wi-Fi.

Why shadow IT occurs: Attention is needed for overseas branches and small-scale offices!
The main reasons given for why shadow IT occurs at overseas branches and small-scale offices is as follows:
Reason1
Completion of work is given top priority
Shadow IT can occur due to a strong sense of responsibility to complete one’s work, blinding one to the fact that they are introducing security risks. Engineer A may have been overly focused on completing his work, causing him to use a personal Wi-Fi router without meaning harm. Particularly at small-scale workplaces, employee relationships tend to become casual, and it is easy for the bringing in of personal devices to become tolerated behavior.

Reason2
Efficiency is prioritized
There are cases where people use private endpoints so they can use the software they want, or they use remote access in ways they aren’t supposed to, in order to do their work more efficiently, but create security risks in doing so.
Reason3
A lack of IT administrators causing insufficient management and awareness
At small-scale workplaces, there are many cases where the main business goals receive most attention, leading to an insufficient number of people managing security. Or, there is no IT administrator at all, or they hold multiple roles, with the result that security awareness is left lacking, and employees do things like share what was supposed to be a limited-use Wi-Fi password.
What security measures are appropriate for overseas branches and small-scale offices?
A cloud is optimal for central managing a unified security policy for all your sites
To construct an authorization server on-premises, establishing network circuits with each site, setting up systems and organizing management costs lots of both time and money. By using a cloud, though, management can be initiated quickly and cheaply, even covering small sites with, for example, fewer than 10 endpoints.
By choosing a service that allows central management by a cloud, policy settings can be set smoothly from your company headquarters, allowing you to reduce operation costs, making a cloud the optimal choice for managing the security of overseas and small-scale sites.

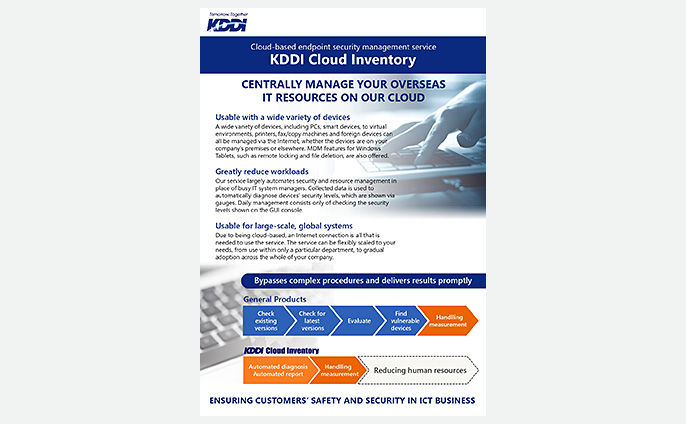
To stop shadow IT, look to KDDI Cloud Inventory’s “Unauthorized device detection” option!
KDDI Cloud Inventory’s “Unauthorized device detection” option solves the following concerns:
- You’ve installed KDDI Cloud Inventory, but you don’t know if all your company endpoints have it installed
- Your company has many locations, and installing and managing an on-premises solution would be costly
- You’re unable to ascertain how many personal endpoints are being used at your company
- Setting up authorization servers at each of your company sites would be costly
- You want to manage your company’s IoT devices but don’t know how
With this option you can detection private endpoints and other devices not being managed by KDDI Cloud Inventory (a tool for management of IT assets and security) and stop those devices from connecting to your company network. This can be easily done from the cloud by just installing a small-size piece of hardware called a LAP sensor within your company network. This LAP sensor works with KDDI Cloud Inventory to check if connecting endpoints are authorized or not, and only permits those that are.
Other columns
No results found
Brochures
What is the best solution for your problem?
Please consult a KDDI consultant.